
|
Cybertelecom Federal Internet Law & Policy An Educational Project |
IPv6

|
IPv6 |
 |
|
Internet Addresses - DNS - History - NTIA & Fed Activity - ICANN - IANA - Root Servers - ccTLDs - - .us - - -.kids.us - gTLDs - - .gov - - .edu - - .mil - - .xxx - WHOIS - WGIG - ENUM - IP Numbers - - IPv6 - BGP - NATs - Ports - Security - Trademark - AntiCybersquatter Consumer Protection Act - Gripe Sites - Truth in Domain Names Telephone Addresses |
Host to Host
1969-70NCP
1970-82TCP/IP v4
1983 - ??IPv6
1996 - ??Derived From: GAO, Internet Protocol version 6, Federal Agencies Need to Plan for Transition and Manage Security Risks, p. 11 - 17 (May 2005)
Every "host" (computer) on the Internet requires an IP number in order to interact over the network. The current number space is IP version 4 (IPv4) and it [has run] out of numbers. In recognition of this limitation, in 1991, work was initiated on a next generation internet protocol. This work resulted in a new address space, IPv6 ("The name IPv5 had previously been allocated to an experimental stream protocol." [NIST Security 2010 p 2-1]). IPv6 dramatically increases the amount of IP address space available from the approximately 4.3 billion addresses in IPv4 to approximately 3.4 × 1038. Because IPv6 uses a 128-bit address scheme rather than the 32-bit address scheme used in IPv4, it is able to allow many more possible addresses. The increase in the actual bits in the address and the immense number of possible combinations of numbers make the dramatic number of unique addresses a possibility. Figure 4 shows the difference between the length of an IPv4 address and that of an IPv6 address.
The key benefits of IPv6 include
- a dramatic increase in IP address space,
- a simplified IP header for flexibility and functionality,
- improved routing of data, [But see Bush Slide 12 (it is a myth that IPv6 reduces routing load)]
- enhanced mobility features,
- easier configuration capabilities,
- improved quality of service, and
- integrated Internet protocol security. [But see Bush Slide 12 (it is a myth that IPv6 has better security)]
Some things that IPv6 does not do include eliminate NATs. [Bush Slide 11] NATs may serve as part of a transition solution. IPv6 also does not eliminate the need for CIDR. [COOK]
These key characteristics of IPv6 offer various enhancements relative to IPv4 and are expected to increase Internet services and enable advanced Internet communications that could foster new software applications for federal agencies.

This large number of IPv6 addresses means that almost any electronic device can have its own address. While IP addresses are commonly associated with computers, they are increasingly being assigned to communications devices such as phones and other items such as consumer electronics and automobiles. -IPv6 addresses are characterized by a network prefix that describes the location of an IPv6-capable device in a network and an interface ID that provides a unique identification number (ID) for the device. The network prefix will change based on the user’s location in a network, while the interface ID can remain static. The static interface ID allows a device with a unique address to maintain a consistent identity despite its location in a network. In IPv4, the limited address space has resulted in a plethora of network address translation devices, which severely limits the possibilities for end-to-end communications. In contrast, the massive address space available in IPv6 will allow virtually any device to be assigned a globally reachable address. This change fosters greater end-to-end communication
abilities between devices with unique IP addresses and can better support the delivery of data-rich content such as voice and video.Simplifying the IPv6 header promotes flexibility and functionality for two reasons. First, the header size is fixed in IPv6. In the previous version, header sizes could vary, which could slow routing of information. Second, the structure of the header itself has been simplified. While the IPv6 addresses are significantly larger than in IPv4, the header containing the address and other information about the data being transmitted has been simplified. The 14 header fields from IPv4 have been simplified to 8 fields in IPv6. Figure 5 illustrates the differences between the two IP headers, including the various data fields that were eliminated, renamed, or reorganized.
Another benefit of the simplified header is its ability to accommodate new features, or extensions. For example, the next header field provides instructions to the routers transmitting the data across the Internet about how to manage the information.
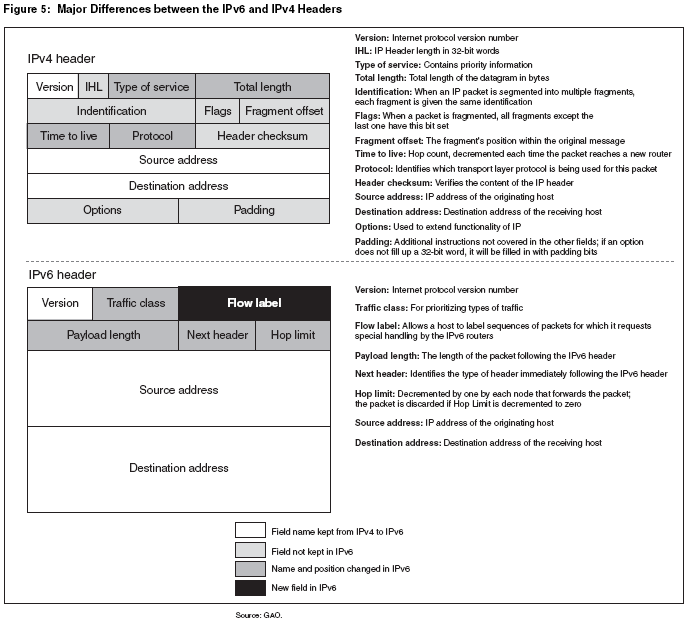
The improved routing, or movement of information from a source to a destination, is more efficient in IPv6 because it incorporates a hierarchal addressing structure and has a simplified header. The large amount of address space allows organizations with large numbers of employees to obtain blocks of contiguous address space. Contiguous address space allows organizations to aggregate addresses under one prefix for identification on the Internet. This structured approach to addressing reduces the amount of information Internet routers must maintain and store and promotes faster routing of data. In addition, as shown in figure 5, IPv6 has a simplified header because of the elimination of six fields from the IPv4 header. The simplified header also contributes to faster routing. -Note: Scalable routing is listed as a concern with IPv6; that IPv6 with its massive increase in IP addresses will create increased demands on routing and routers - to the point where the increased demands become problematic.
|
NRO IPv6 Educational Video |
|
Martin Levy on Hurricane Electric before RIPE NCC |
IPv6 improves mobility features by allowing each device (wired or wireless) to have a unique IP address independent of its current point of attachment to the Internet. As previously discussed, the IPv6 address allows computers and other devices to have a static interface ID. The interface ID does not change as the device transitions among various networks. This enables mobile IPv6 users to move from network to network while keeping the same unique IP address. The ability to maintain a constant IP address while switching networks is cited as a key factor for the success of a number of evolving capabilities, such as evolving telephone technologies, personal digital assistants, laptop computers, and automobiles. -IPv6 enhancements can ease difficult and time-consuming aspects of network administration tasks in today’s IPv4 networks. For example, two new configuration enhancements of IPv6 include automatic address configuration and neighbor discovery. These enhancements may reduce network administration burdens by providing the ability to more easily deploy and manage networks.
IPv6 supports two types of automatic configuration: stateful and stateless. Stateful configuration uses the dynamic host configuration protocol. This stateful configuration requires another computer, such as a server, to reconfigure or assign numbers to network devices for routing of information, which is similar to how IPv4 handles renumbering. Stateless automatic configuration is a new feature in IPv6 and does not require a separate dynamic host configuration protocol server as in IPv4.
Stateless configuration occurs automatically for routers and hosts. Another configuration feature—neighbor discovery—enables hosts and routers to determine the address of a neighbor or an adjacent computer or router.
Together, automatic configuration and neighbor discovery help support a plug-and-play Internet deployment for many devices, such as cell phones, wireless devices, and home appliances. These enhancements help reduce the administrative burdens of network administrators by allowing the IPv6- enabled devices to automatically assign themselves IP addresses and find compatible devices with which to communicate.
IPv6’s enhanced quality of service feature can help prioritize the delivery of information. The flow label is a new field in the IPv6 header. This field can contain a label identifying or prioritizing a certain packet flow, such as a video stream or a videoconference, and allows devices on the same path to read the flow label and take appropriate action based on the label. For example, IP audio and video services can be enhanced by the data in the flow label because it ensures that all packets are sent to the appropriate destination without significant delay or disruption.
IP Security—a means of authenticating the sender and encrypting the transmitted data—is better integrated into IPv6 than it was in IPv4. This improved integration, which helps make IP Security easier to use, can help support broader data protection efforts. [But see Bush Slide 12 (it is a myth that IPv6 has better security)] [Underwood ("IPSEC, invented for IPv6 is in every IPv4 implementation")]
IP Security consists of two header extensions that can be used together or separately to improve authentication and confidentiality of data being sent via the Internet. The authentication extension header provides the receiver with greater assurance of who sent the data. The encapsulating security header provides confidentiality to messages using encrypted security payload extension headers.
IPv6’s increased address space, functionality, flexibility, and security help to support more advanced communications and software applications than are thought to be possible with the current version of IP. For example, the ability to assign an IP address to a wide range of devices beyond computers creates many new possibilities for direct communication. While applications that fully exploit IPv6 are still in development, industry experts have identified various federal functions that might benefit from IPv6-enabled applications:
- Border security: could deploy wireless sensors with IPv6 to help provide situational awareness about movements on the nation’s borders.
- First responders: could exploit the hierarchal addressing of IPv6 to promote interoperability and rapid network configuration in responding to emergencies.
- Public health and safety: could exploit IPv6 end-to-end communications to deliver secure telemedicine applications and interactive diagnoses.
- Information sharing: could benefit from various features of IPv6, including securing data in end-to-end communications, quality of service, and the extensibility of the header to accommodate new functions
Barriers to Transition:
Cost. It is a substantial investment which profit sensitive companies are inclined to put off. [AT&T: New Gen of the IP] [NIST Economic Impact Assessment]
Trained Staff: Hiring staff trained and experienced with IPv6.
Incentives: As long as there are some IPv4 numbers available, the incentive to migrate to IPv6 is limited.
Network Effect: IPv6 networks can only reach IPv6 assets (absent some transition kludge). Therefore, if there are few resources available on the Net that can be reached by an IPv6 network, there is little incentive to transition. At some point this will tip, where there are sufficient resources on IPv6 networks and the network effect is sufficiently valuable to create an incentive to transition.
Security:
Derived From: Potential Impacts on Communications from IPv4 Exhaustion & IPv6 Transition Robert Cannon, OSP, December 2010 Paper: Word | Acrobat |
IPv6 is a new network protocol which will require new training, experience, and implementations. During the transition, new vulnerabilities could be introduced, and IPv4 security devices and software may be of limited use. 1As network operators have done when introducing anything new into networks, operators will have to work with and test IPv6 implementations in order to ensure security. 2
1Michael Warfield, Internet Security Systems, Security Implications of IPv6 (2003) ("IPv6 is not a panacea for security, though, because few security problems derive solely from the IP layer in the network model. For example, IPv6 does not protect against misconfigured servers, poorly designed applications, or poorly protected sites. In addition, IPv6 and IPv6 transitional mechanisms introduce new, not widely understood, tools and techniques that intruders can use to secure unauthorized activity from detection. These IPv6-derived efforts are often successful even against existing IPv4 networks.").
2See Planning Guide/Roadmap Toward IPv6 Adoption within the US Government, The Federal CIO Council Architecture and Infrastructure Committee Technology Infrastructure Subcommittee Federal IPv6 Working Group, p. 34 (May 2009); OECD Study: Economic considerations in the management of IPv4 and in the deployment of IPv6, p. 42 (May 2008).
. See NIST IPv6 Security Documentation.
Derived From: NIST Security 2010 p ES-1
Networks "will most likely face security challenges throughout the deployment process, including:
- "An attacker community that most likely has more experience and comfort with IPv6 than an organization in the early stages of deployment
- "Difficulty in detecting unknown or unauthorized IPv6 assets on existing IPv4 production networks
- "Added complexity while operating IPv4 and IPv6 in parallel
- "Lack of IPv6 maturity in security products when compared to IPv4 capabilities
- "Proliferation of transition-driven IPv6 (or IPv4) tunnels, which complicate defenses at network boundaries even if properly authorized, and can completely circumvent those defenses if unauthorized (e.g. host-based tunnels initiated by end users)"
"Organizations that are not yet deploying IPv6 globally should implement the following recommendations:
- "Block all IPv6 traffic, native and tunneled, at the organization's firewall. Both incoming and outgoing traffic should be blocked.
- "Disable all IPv6-compatible ports, protocols and services on all software and hardware.
- "Begin to acquire familiarity and expertise with IPv6, through laboratory experimentation and/or limited pilot deployments.
- "Make organization web servers, located outside of the organizational firewall, accessible via IPv6 connections. This will enable IPv6-only users to access the servers and aid the organization in acquiring familiarity with some aspects of IPv6 deployment.
"Organizations that are deploying IPv6 should implement the following recommendations to mitigate IPv6 threats:
- "Apply an appropriate mix of different types of IPv6 addressing (privacy addressing, unique local addressing, sparse allocation, etc) to limit access and knowledge of IPv6-addressed environments.
- "Use automated address management tools to avoid manual entry of IPv6 addresses, which is prone to error because of their length.
- "Develop a granular ICMPv6 (Internet Control Protocol for IPv6) filtering policy for the enterprise. Ensure that ICMPv6 messages that are essential to IPv6 operation are allowed, but others are blocked.3
- "Use IPsec (Internet Protocol Security) to authenticate and provide confidentiality to assets that can be tied to a scalable trust model (an example is access to Human Resources assets by internal employees that make use of an organization's Public Key Infrastructure (PKI) to establish trust).
- "Identify capabilities and weaknesses of network protection devices in an IPv6 environment.
- "Enable controls that might not have been used in IPv4 due to a lower threat level during initial deployment (implementing default deny access control policies, implementing routing protocol security, etc).
- "Pay close attention to the security aspects of transition mechanisms such as tunneling protocols.
- "Ensure that IPv6 routers, packet filters, firewalls, and tunnel endpoints enforce multicast scope boundaries and make sure that Multicast Listener Discovery (MLD) packets are not inappropriately routable.
- "Be aware that switching from an environment in which NAT (Network Address Translation) provides IP (Internet Protocol) addresses to unique global IPv6 addresses could trigger a change in the FISMA (Federal Information Security Management Act) system boundaries.
ITL Security Bulletin January 2011 - Internet Protocol Version 6 (Ipv6): NIST Guidelines Help Organizations Manage The Secure Deployment Of The New Network Protocol January2011-ITLBulletin.pdf
Law Enforcement
Derived From: Potential Impacts on Communications from IPv4 Exhaustion & IPv6 Transition Robert Cannon, OSP, December 2010 Paper: Word | Acrobat |
The transition to IPv6 creates concerns for law enforcement. During the transition, kludges will be employed by networks in order to conserve addresses and allow networks to keep expanding. These solutions, however, break end-to-end connectively and make it difficult to map specific IP numbers to individual end users. IP numbers may map to carrier grade NAT boxes which may have behind them many households, neighborhoods, or even towns, making it difficult to know to whom an IP address belongs. 10 Law enforcement has also expressed concern that WHOIS 20 for IPv6 contain accurate and useful information. ISPs may incur additional administrative burdens of having to retain records of the dynamic mapping between addresses. 30 There may also be issues with CALEA compliance. The ARIN Government Working Group has been working on these issues. 40
10See M. Ford, M. Boucadair, A. Durand, P. Levis, P. Roberts, Issues with IP Address Sharing , IETF Informational Draft (Mar. 8, 2010).
20See, e.g. , Internet Management: Prevalence of False Contact Information for Registered Domain Names , GAO-06-165 (Nov. 2005); Lennard G. Krugar, Internet Domain Names: Background and Policy Issues, Congressional Research Service (Oct. 28, 2009)
30See Jason Weil, COX, Service Provider NAT44 Overview, NANOG50, slide 5 (October 2010).
40See ARIN XXV Public Policy Meeting Day 1 Notes - 19 April 2010; ARIN XXIII Public Policy Meeting Day 2 Notes - 28 April 2009 (noting work of ARIN Government Working Group, mentioning Bobby Flaim, FBI, and Marc Moreau, Royal Canadian Mounted Police); ARIN Government Working Group (AGWG) (Apr. 2009); Supervisory Special Agent Robert Flaim, Law Enforcement and Internet Governance: "An Ounce of Prevention is Worth a Pound of Cure," AfriNIC Government Working Group Meeting Nov. 26, 2010.
Next >> IPv6 Transition.
© Cybertelecom ::